pendragon1
Extremely [H]
- Joined
- Oct 7, 2000
- Messages
- 52,122
Last edited:
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
What some conspiracy theory now? Everyone and their mother suspects Russia via APT29/SVR ie Cosy Bear.russia is the scapegoat.
go to the thread in soapbox.What some conspiracy theory now? Everyone and their mother suspects Russia via APT29/SVR ie Cosy Bear.
I don't have a key to that hole.go to the thread in soapbox.
get a sub, its $5 and supports the site.I don't have a key to that hole.
Yeah i get it a ddll with a backdoor on orion which is not clould but I also get "we do not know..." - That's my point.Mega6 yes, not yet but from what we do know, the facts so far is that, it is a dll, it is only Orion on -prem so far and also what ever comes from their M365 being compromised. Unless they update their hosted cloud platform from the same repo's they use for customers on prem....then cloud should not be affected via this specific method, but we do not know that either.
It looks like like Microsoft uses the tool and they ARE a Cloud provider. We can only assume everything Microsoft has been compromised without any confirmation of the extent of the damagethat's one portion of solarwinds. it's an on-premises based solution for application and infra monitoring. you clearly have no idea about it. I have first hand experience, over a decade, using the tool.
Cloud is just someone else's server. That Cloud provider will still have people going to the data centerThe cloud is as secure as Windows or Linux or your Intel or AMD hardware. The people, processes, and technology around what you do with any of that stuff is what leads to security. No silver bullet exists - i.e. "let's move to the cloud" for security. People move to the cloud so they can have elastic workloads, economies of scale, and because the whole damn country has been in semi-lockdown for 8 months+ and the server monkeys can't go into data centers.
Oh how convienent, Dominion Software is not listed.It is going to be a fun couple weeks.....
You wonder how many of their customers who have to spend time and resources rebuilding will be sending Solarwinds and big fat bill for them to pay for it..
https://krebsonsecurity.com/2020/12...e-depts-hacked-through-solarwinds-compromise/
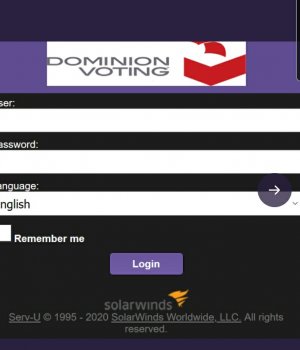
View attachment 309099
I personally know of 2 other large companies that were compromised by the hack after speaking with a few industry peers and vendors. However, they haven't gone public about it so I cannot comment. (also, I'm an InfraGard contributor and NITSL/USA member)I mean they said less ~18k customers downloaded the compromised version.
They’ve only listed the federal agencies that have self reported as downloading the compromised version. So still plenty of enterprises pwned.
SolarWinds exposed their FTP server credentials in a public Github repo
https://savebreach.com/solarwinds-credentials-exposure-led-to-us-government-fireye-breach/Credentials of the FTP download server which was exposed on the SolarWinds GitHub repo are as follows – solarwindsnet:solarwinds123
[FYI - be careful on the sources that you trust and be sure to read into what they're saying - they use words like "possible" and source random twitter users. I have not seen this validated yet but any security researchers...that said it could easily be true and does not make this hack any more simple - this is just the breach component]It seems the attackers weren't that sophisticated after all.
https://savebreach.com/solarwinds-credentials-exposure-led-to-us-government-fireye-breach/
So they just walked in through the front door. That level of capability is not limited to APTs.
oh wow!It seems the attackers weren't that sophisticated after all.
https://savebreach.com/solarwinds-credentials-exposure-led-to-us-government-fireye-breach/
So they just walked in through the front door. That level of capability is not limited to APTs.
It seems the attackers weren't that sophisticated after all.
https://savebreach.com/solarwinds-credentials-exposure-led-to-us-government-fireye-breach/
So they just walked in through the front door. That level of capability is not limited to APTs.
You wouldn't believe some of the passwords major cyber security vendors use. It isn't just SolarWinds. I see it first hand when I have to work with some of them.. some of the passwords are even hard coded into an executable with dependencies, so you have to recompile programs or modify database server backends to change passwords. It's a leftover from their legacy implementations 15+ years ago that never have updated the core underlying source code. I've seen some that even use 3 and 4 digit numerical passcodes instead of actual passwords.OMG. Their password was solarwinds123
How does this happen? How utterly incompetent can an enterprise network solutions provider be?
If they can't even get this right, they deserve every bit of business loss they get out of this thing.
You wouldn't believe some of the passwords major cyber security vendors use. It isn't just SolarWinds. I see it first hand when I have to work with some of them.. some of the passwords are even hard coded into an executable with dependencies, so you have to recompile programs or modify database server backends to change passwords. It's a leftover from their legacy implementations 15+ years ago that never have updated the core underlying source code. I've seen some that even use 3 and 4 digit numerical passcodes instead of actual passwords.
I've submitted CR fixes and bug reports for years to the vendors.. they just get closed saying they'll fix it in the next major product version, which it never does.Jesus Christ.
At the very least the people who have to use those passwords on a semi-regular basis should be aware this isn't good, and report it up the chain until it gets fixed.
It's one thing if you are logging into some stupid shit like Animal Crossing or something like that. It's something different all together if your software is deeply integrated with large companies around the world, and if it gets pwned, they might get pwned too.
I still say this is inexcusable.
If anything, this is a motivation to go all open source, and ditch all the "appliances in a box". I haveno idea hwy IT departments keep buying that garbage. It is always slower, more expensive and less secure to - say - get a Sonicwall box, than it is to just run a pfSense box. IMHO, whenhever possible, always pass on specialized "solution in a box, with hardware", and use your own server instead.
I've submitted CR fixes and bug reports for years to the vendors.. they just get closed saying they'll fix it in the next major product version, which it never does.
The thing about passwords is users have to remember them. Complex password requirements with double-digit characters seem great to people trying to prevent brute force password hacks. Telling people not to reuse passwords sounds good. In reality they fail because the user has to, you know, USE the system and needs to remember that password plus 8 others for work, plus 30 others for daily life (one for every streaming service, shopping website, bank account, credit card, gaming service, utility bill, mortgage/rent, ad nauseum). I'd like to think I'm pretty smart and can remember a lot of stuff, but that's fucking impossible.
The organization I work for adopted the NIST password requirements of 15+ characters, at least 1 capital letter, 1 lower case letter, 1 number, and 1 special character. Then NIST realized "You know what? That's fucking ridiculous and unusable" and dropped their password recommendations. I still have to remember 15 character passwords.
I mean the very first paragraph in Solarwinds security advisory...what does this have to do with the cloud specifically?
Now I don't have a decades worth of firsthand experience, but I don't think the hackers are coming to the premises to pick up a print-out of the compromised info.SolarWinds has been made aware of a cyberattack to our systems that inserted a vulnerability within our SolarWinds® Orion® Platform software builds for versions 2019.4 HF 5, 2020.2 with no hotfix installed, and 2020.2 HF 1, which, if present and activated, could potentially allow an attacker to compromise the server on which the Orion products run.
BREAKING REPORT: Feds Arrive at SolarWinds HQ in Austin — More News Coming on CEO and Executive Vice President — New Update = https://www.thegatewaypundit.com/20...angers-us-marshals-raid-solarwinds-hq-austin/Solar Winds, what a great game it was! Ah, the memories!
https://www.dosgamesarchive.com/download/solar-winds/
This company and board are toast.
"Yeah, the sheer scale and breadth of the attack will make a lot of powerful people/entities want justice. You don't piss off the people with the money and the power. If it was one of us - yeah, slap on the wrist if they stole from us or leaked our data (hello: Equifax).