- Joined
- Mar 3, 2018
- Messages
- 1,713
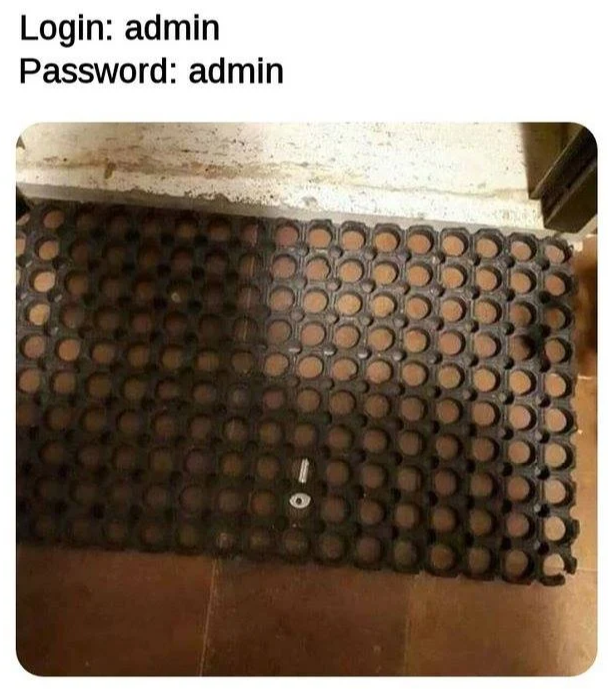
Security researchers discovered an exploit that allows attackers to gain administrative access to WD My Cloud NAS devices. Simply having a cookie with the string "username = admin" when the device sends a login request will allow you to run administrative commands, such as reading or deleting files, without needing a password. The researchers tested proof of concept code on a model WDBCTL0020HWT NAS, but say the exploit works on most products in the My Cloud series. When it comes to responding to vulnerabilities, WD has a spotty track record, but thankfully they claim a patch for this exploit will be out in the coming weeks. Thanks to tikiman2012 for the tip.
It was found that it is possible for an unauthenticated attacker to create a valid session without requiring to authenticate. The network_mgr.cgi CGI module contains a command called cgi_get_ipv6 that starts an admin session that is tied to the IP address of the user making the request when invoked with the parameter flag equal to 1. Subsequent invocation of commands that would normally require admin privileges are now authorized if an attacker sets the username=admin cookie.
It was found that it is possible for an unauthenticated attacker to create a valid session without requiring to authenticate. The network_mgr.cgi CGI module contains a command called cgi_get_ipv6 that starts an admin session that is tied to the IP address of the user making the request when invoked with the parameter flag equal to 1. Subsequent invocation of commands that would normally require admin privileges are now authorized if an attacker sets the username=admin cookie.
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)