Not sure my setup is correctly implemented but I am trying to have one-way communications to a VLAN for cameras.
Need to isolate camera network (VLAN3) from accessing the internet or any other internal network but I need to be able to reach into the VLAN3 network.
Right now, the only way I can access VLAN3 is by putting a persistent static route in my laptops routing table. Is there a way to set this in pfSense? I tried creating a static route in pfSense but I am getting a "Time to Live Exceeded" error when pinging 192.168.3.x. I tried using 192.168.1.1 as the gateway to access 192.168.3.0
Should my Gateway in pfSense be 192.168.1.250 (the IP of the Brocade switch)? I can't figure out a way to set that up in pfSense. There is no option for this.
Here is my Brocade access-list:
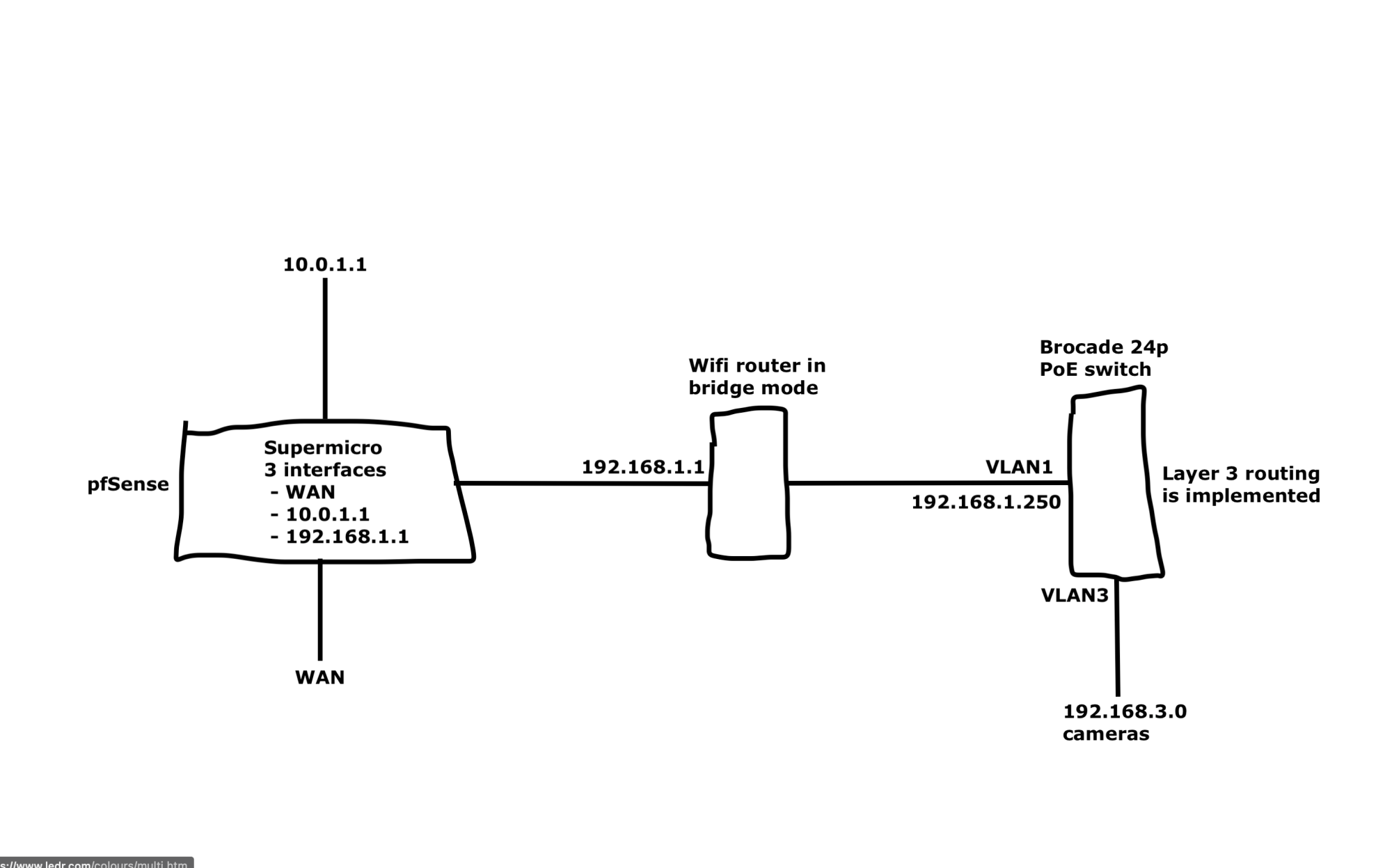
Need to isolate camera network (VLAN3) from accessing the internet or any other internal network but I need to be able to reach into the VLAN3 network.
Right now, the only way I can access VLAN3 is by putting a persistent static route in my laptops routing table. Is there a way to set this in pfSense? I tried creating a static route in pfSense but I am getting a "Time to Live Exceeded" error when pinging 192.168.3.x. I tried using 192.168.1.1 as the gateway to access 192.168.3.0
Should my Gateway in pfSense be 192.168.1.250 (the IP of the Brocade switch)? I can't figure out a way to set that up in pfSense. There is no option for this.
Here is my Brocade access-list:
Here is my network diagram:access-list 100 remark ALLOW ESTABLISHED TCP TRAFFIC
access-list 100 permit tcp any any established
access-list 100 remark ALLOW VLAN3 TO RESPOND TO PING
access-list 100 permit icmp 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255 echo-reply
access-list 100 remark ALLOW CAMERAS TO TALK TO NVR
access-list 100 permit ip 192.168.3.0 0.0.0.255 192.168.3.0 0.0.0.255
access-list 100 remark DENY VLAN3 TO RFC1918
access-list 100 deny ip 192.168.3.0 0.0.0.255 any
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)