viper1152012
[H]ard|Gawd
- Joined
- Jun 20, 2012
- Messages
- 1,025
The short window of review and being unverified make me wanna eat a whole bottle of salt when I read the article.
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
Surely those security experts that found it work for free and only have AMD owner's best interest at heart."The researchers gave AMD less than 24 hours to look at the vulnerabilities and respond before publishing the report. Standard vulnerability disclosure calls for 90 days' notice so that companies have time to address flaws properly."
https://www.cnet.com/news/amd-has-a-spectre-meltdown-like-security-flaw-of-its-own/#
Another article covering the topic, if true this to me points to a marketing and smear campaign rather than a legitimate independent security research. In any case, who paid for the research? that is not covered in their legal disclaimer or any information in the white paper.
Trivial with Windows install media. Boot to a recovery command prompt, replace the login screen Ease of Access executable with cmd.exe, reboot. Once booted, open the command prompt, pass 'net user' to list local user accounts, pick one and reset the password. Done. Also any number of free boot disks have utilities that mount NTFS, find the user store, query it for admin level users, and then blank the password (and optionally enable the account if disabled). Some of these methods might be hindered by full disk encryption, Bitlocker, or other measures, I can't claim to have tested any mitigations for this particular attack.The way I see it, if you have access to a machine already, gaining elevated rights will be a small cake walk for some. Nothing I can pull off, but many others will.
Actually going through a red team inspection right now.
Not only that, I think Intel is losing market share. Intel doing this is a good way to neutralize AMD, or at least slow down their advance. Fear based marketing still works. I for one won't upgrade my intel chip, until I absolutely have too, til I see a permanent redesigned chip without the flaws. That is one news item I have not read about. It takes yrs to do design work, so Intel give me some good news on a permanent flaw free new chip.Probably an Intel smear campaign. I believe all these exploits need root access or physical access to hardware.
Trivial with Windows install media. Boot to a recovery command prompt, replace the login screen Ease of Access executable with cmd.exe, reboot. Once booted, open the command prompt, pass 'net user' to list local user accounts, pick one and reset the password. Done. Also any number of free boot disks have utilities that mount NTFS, find the user store, query it for admin level users, and then blank the password (and optionally enable the account if disabled). Some of these methods might be hindered by full disk encryption, Bitlocker, or other measures, I can't claim to have tested any mitigations for this particular attack.
Either method is something that anyone with Google and a boot disk can get done in ~10 minutes or less.
OK, just for the sake of argument, let's say that everything they claim is true. It could still be a smear campaign. Just highly exaggerate the claims and word them to make things look as grim as possible. Then release the "report" with little or no warning to the victim, and use a website that can't be traced back to original authors. And the icing on the cake is to create a new company in another country to be the front for the effort. Using these techniques I could smear Mother Theresa. When people use highly unethical methods, you must question their "facts". When you look at their claims, you find that they all require a highly compromised system (administrator privileges, relflashing the BIOS with a "custom" version, using a modified and signed device driver) to use any of the exploits identified. Once a system is that compromised, you are screwed anyway, regardless of the underlying hardware.
Think you mean local attacks. Which is exactly what Meltdown is also.
Trivial with Windows install media. Boot to a recovery command prompt, replace the login screen Ease of Access executable with cmd.exe, reboot. Once booted, open the command prompt, pass 'net user' to list local user accounts, pick one and reset the password. Done. Also any number of free boot disks have utilities that mount NTFS, find the user store, query it for admin level users, and then blank the password (and optionally enable the account if disabled). Some of these methods might be hindered by full disk encryption, Bitlocker, or other measures, I can't claim to have tested any mitigations for this particular attack.
Either method is something that anyone with Google and a boot disk can get done in ~10 minutes or less.
This is false, Meltdown is demonstrated remotely in javascript.
Spectre too, Spectre was never demonstrated to work on amd chips, but in theory they should be able to work.
In theory white holes (opposite of black holes) do exist but we don't see something bright pushing out material at amazing rates but they might exist.
But spectre and meltdown does not require local attack vector.
Local execution.This is false, Meltdown is demonstrated remotely in javascript.
Spectre too, Spectre was never demonstrated to work on amd chips, but in theory they should be able to work.
In theory white holes (opposite of black holes) do exist but we don't see something bright pushing out material at amazing rates but they might exist.
But spectre and meltdown does not require local attack vector.
PCWorld is more like CNN ever day.https://www.pcworld.com/article/326...ipset-have-major-flaws-researchers-claim.html
The idiots are already spreading it.
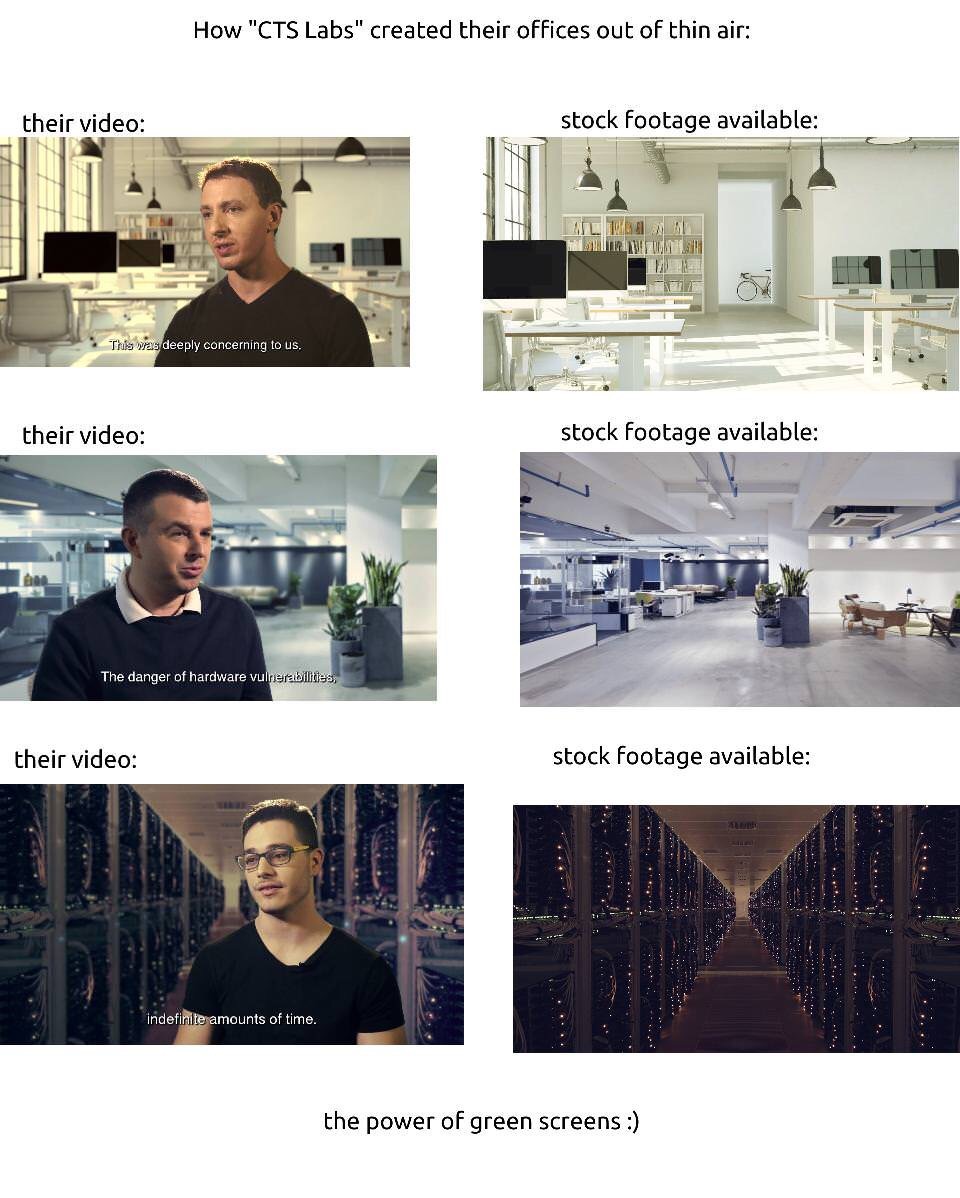
The chaotic nature of today's disclosure has led to many questions about the source and motivations of the firms behind this research. Astute social-media users have noted that Viceroy Research, a financial-analysis group that reportedly engages in short selling of various companies' securities, appears to have coordinated the release of a report provocatively titled "The Obituary" alongside the CTS Labs whitepaper. Viceroy posits that AMD will have no choice but to file for Chapter 11 bankruptcy as a result of the news and that its stock is ultimately worthless, claims that seem vastly out of proportion with the magnitude of the purported vulnerabilities that CTS Labs has discovered.
Still betting this is AMD short-sellers trying to manipulate the market, not Intel.
AMD stock is still up on the day (though less so than earlier)
I'm thinking more from AD domain, not so much just getting local admin rights on a machine. An MS Dart disc can get me local admin access, so long as I have physical access.
Meltdown is demonstrated remotely in javascript using a local attack. As in, someone locally, on the machine, executes it. That's what local attack means. It's not some hacker on the net, using the Meltdown vulnerability to gain access to the box.
Wired has a good article on this - Overblown to say the least.
"four attacks require administrative privileges means that to execute them, a hacker would already need extraordinary access to a device—and could presumably already create all kind of havoc even without Ryzenfall, Masterkey, Fallout, or Chimera."
https://www.wired.com/story/amd-backdoor-cts-labs-backlash/
While CTS hasn't publicly released any of the details of how its attacks work, it did share them privately with New York-based security firm Trail of Bits, which essentially confirmed the central findings. "Regardless of hype, they found vulnerabilities that work as described," says Dan Guido, Trail of Bits' founder. "If you’ve already taken over a computer to a certain extent, they'll allow you to expand that access, or to hide in parts of the processors where you didn’t think malware could be."
It smells of Intel.Still betting this is AMD short-sellers trying to manipulate the market, not Intel.
AMD stock is still up on the day (though less so than earlier)
Apparently CTS is paying for news?
https://motherboard.vice.com/en_us/...ssor-ryzen-epyc-vulnerabilities-and-backdoors
tldr: The bugs are real (at least according to the 3rd party CTS paid for confirmation), but the way everything was presented and done is sketchy as hell to say the least. (24 hr disclosure, the report from a stock company saying AMD is worth nothing, and a website describing the bugs in a outrageous manner) I'm calling it a overhyped problem, probably designed to make AMD look bad or do some other shady stock market stuff.