- Joined
- May 18, 1997
- Messages
- 55,634
Update 2: While not confirmed, it looks as if Petya / Petwrap is a fake MS certification to run PSEXEC with stolen/blackmarket SMB logins.
Update: Our in-house security expert is telling me that Petya / Petwrap looks to be a worm with multiple propagation functionality. "The worst I have ever seen. Ever. This is going to be very bad." So far this is looking to affect all Windows OS variants. The latest patch from Microsoft for EternalBlue likely does nothing for Petya. There is no killswitch.
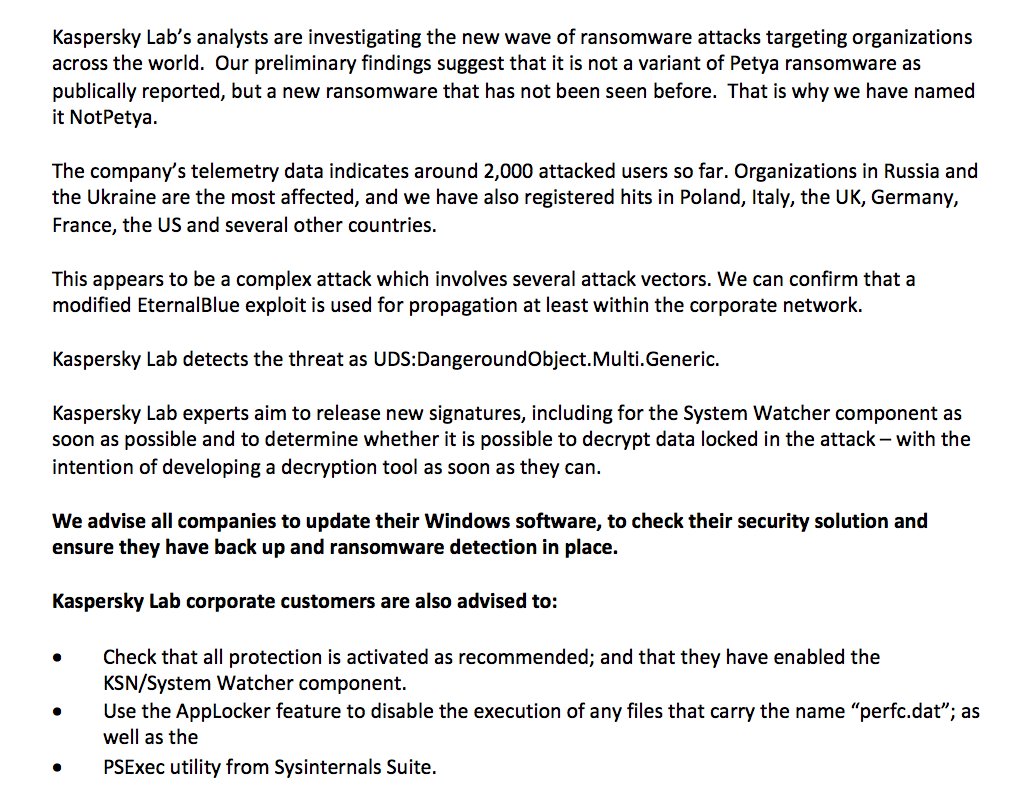
Twitter is alive and well this morning and it seems that a new strain of ransomware known as "Petya" is getting a lot of attention over in the Ukraine and elsewhere. This looks to possibly be a Zero Day exploit (meaning that there is likely no immediate patch for this) that is spinning up much like the Wannacry ransomworm that was just dealt with recently. And others are suggesting that is is simply another SMB protocol exploit. We are waiting for our in-house security expert to give us some insight from his own sandbox. Petya, also known as Petwrap, has already hit Russia Russia Russia, Spain, and France very hard, but is quickly spreading across Europe and Asia. This Ransomware gives a fake ChkDsk screen that appears to run but is actually encrypting your data. The Hacker News has some insight.
Petya is a nasty piece of ransomware and works very differently from any other ransomware malware. Unlike other traditional ransomware, Petya does not encrypt files on a targeted system one by one.
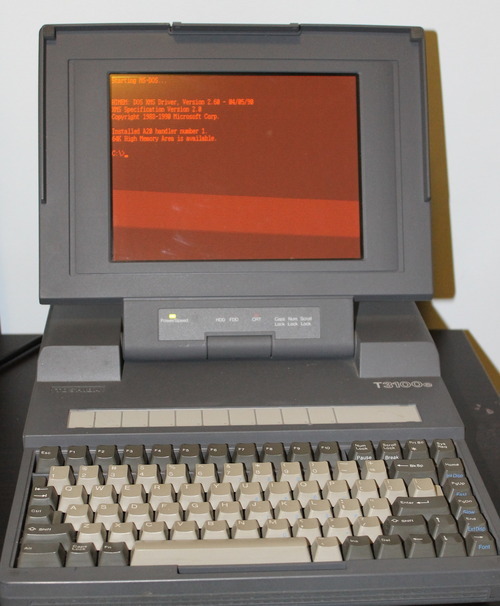
Instead, Petya reboots victims computers and encrypts the hard drive's master file table (MFT) and rendering the master boot record (MBR) inoperable, restricting access to the full system by seizing information about file names, sizes, and location on the physical disk.
Update: Our in-house security expert is telling me that Petya / Petwrap looks to be a worm with multiple propagation functionality. "The worst I have ever seen. Ever. This is going to be very bad." So far this is looking to affect all Windows OS variants. The latest patch from Microsoft for EternalBlue likely does nothing for Petya. There is no killswitch.
Twitter is alive and well this morning and it seems that a new strain of ransomware known as "Petya" is getting a lot of attention over in the Ukraine and elsewhere. This looks to possibly be a Zero Day exploit (meaning that there is likely no immediate patch for this) that is spinning up much like the Wannacry ransomworm that was just dealt with recently. And others are suggesting that is is simply another SMB protocol exploit. We are waiting for our in-house security expert to give us some insight from his own sandbox. Petya, also known as Petwrap, has already hit Russia Russia Russia, Spain, and France very hard, but is quickly spreading across Europe and Asia. This Ransomware gives a fake ChkDsk screen that appears to run but is actually encrypting your data. The Hacker News has some insight.
Petya is a nasty piece of ransomware and works very differently from any other ransomware malware. Unlike other traditional ransomware, Petya does not encrypt files on a targeted system one by one.
Instead, Petya reboots victims computers and encrypts the hard drive's master file table (MFT) and rendering the master boot record (MBR) inoperable, restricting access to the full system by seizing information about file names, sizes, and location on the physical disk.
Last edited:
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)