The Lurker
Fully [H]
- Joined
- Jul 1, 2001
- Messages
- 19,085
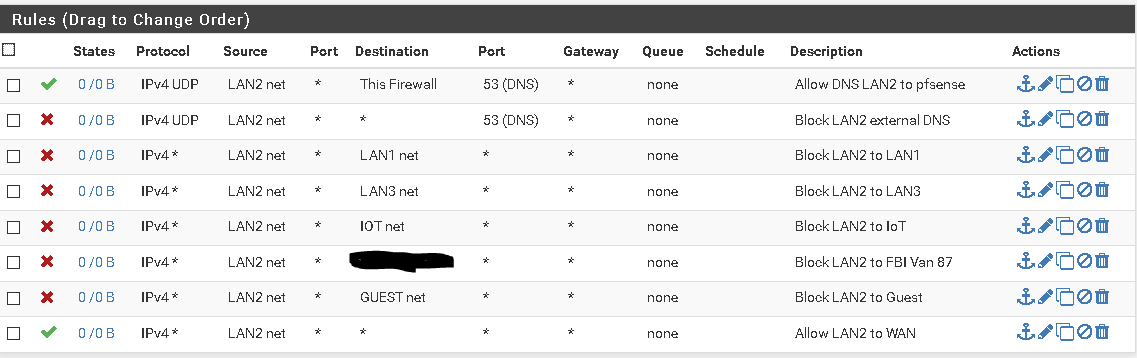
I have been tracking down some errant ADware issues on my home network and I learned that some of my devices were completely bypassing the PFSense DNS resolver. That lead me to finding this link:
https://docs.netgate.com/pfsense/en/latest/recipes/dns-over-tls.html
I am confused between redirecting DNS queries and blocking DNS queries. Both ultimately force the client to query the PfSense resolver, but what is the difference between redirecting and blocking?
While I am here, can someone explain why DNS over HTTPS cannot be blocked on the firewall? I am assuming because it uses the same port as regular traffic and its not possible to tell whats DNS versus everything else.
https://docs.netgate.com/pfsense/en/latest/recipes/dns-over-tls.html
I am confused between redirecting DNS queries and blocking DNS queries. Both ultimately force the client to query the PfSense resolver, but what is the difference between redirecting and blocking?
While I am here, can someone explain why DNS over HTTPS cannot be blocked on the firewall? I am assuming because it uses the same port as regular traffic and its not possible to tell whats DNS versus everything else.
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)