- Joined
- May 18, 1997
- Messages
- 55,601
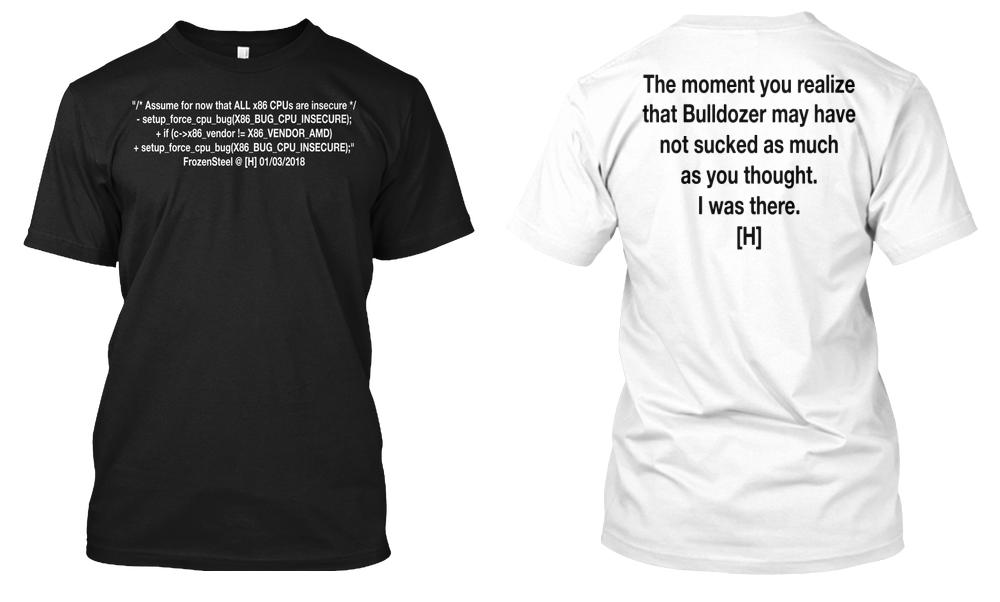
Linus Torvalds on Github has posted a few urgent fixes for PTI to address Intel's gaping security hole that we covered earlier today. Of note in his post is that he is confident in excluding AMD processors from the update as the company has been confident that they are not affected by the bug. Here is what Lisa Su said (auto-start video warning).
Exclude AMD from the PTI enforcement. Not necessarily a fix, but if AMD is so confident that they are not affected, then we should not burden users with the overhead - x86/cpu, x86/pti: Do not enable PTI on AMD processors
UPDATE: Tom Lendacky has made a BIG call!
AMD processors are not subject to the types of attacks that the kernel page table isolation feature protects against. The AMD microarchitecture does not allow memory references, including speculative references, that access higher privileged data when running in a lesser privileged mode when that access would result in a page fault.
Exclude AMD from the PTI enforcement. Not necessarily a fix, but if AMD is so confident that they are not affected, then we should not burden users with the overhead - x86/cpu, x86/pti: Do not enable PTI on AMD processors
UPDATE: Tom Lendacky has made a BIG call!
AMD processors are not subject to the types of attacks that the kernel page table isolation feature protects against. The AMD microarchitecture does not allow memory references, including speculative references, that access higher privileged data when running in a lesser privileged mode when that access would result in a page fault.
Last edited:
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)